Data on the Internet is generally quite secure. Assuming everyone is careful with passwords and other protections, you might think it’s locked in a vault so strong that even all the supercomputers in the world, working together for 10,000 years, can’t crack it.
But last month, Google and others released results suggesting a new type of computer — a quantum computer — might be able to open the vault with significantly fewer resources than previously thought.
The changes come on two fronts. In one, tech giants like IBM and Google are racing to build ever-larger quantum computers: IBM hopes to achieve a real advantage over classical computers in some special cases this year, and an even more powerful “fault-tolerant” system by 2029.
On the other hand, theorists are perfecting quantum algorithms: last job shows the necessary resources to break today’s cryptography may be much lower than previous estimates.
The net result? The day when quantum computers can break widely used cryptography — oddly named “Q Day” — may be coming sooner than expected.
The quantum hardware race
Quantum computers are built from quantum bits, or qubits, which use the counterintuitive properties of very small objects to perform calculations in a different and sometimes much more efficient way than traditional computers.
So far the technology is in its infancy, with the main goal of increasing the number of qubits that can be connected to work as a single computer. Larger quantum computers should be much better at some things than their traditional counterparts – they will have a “quantum advantage”.
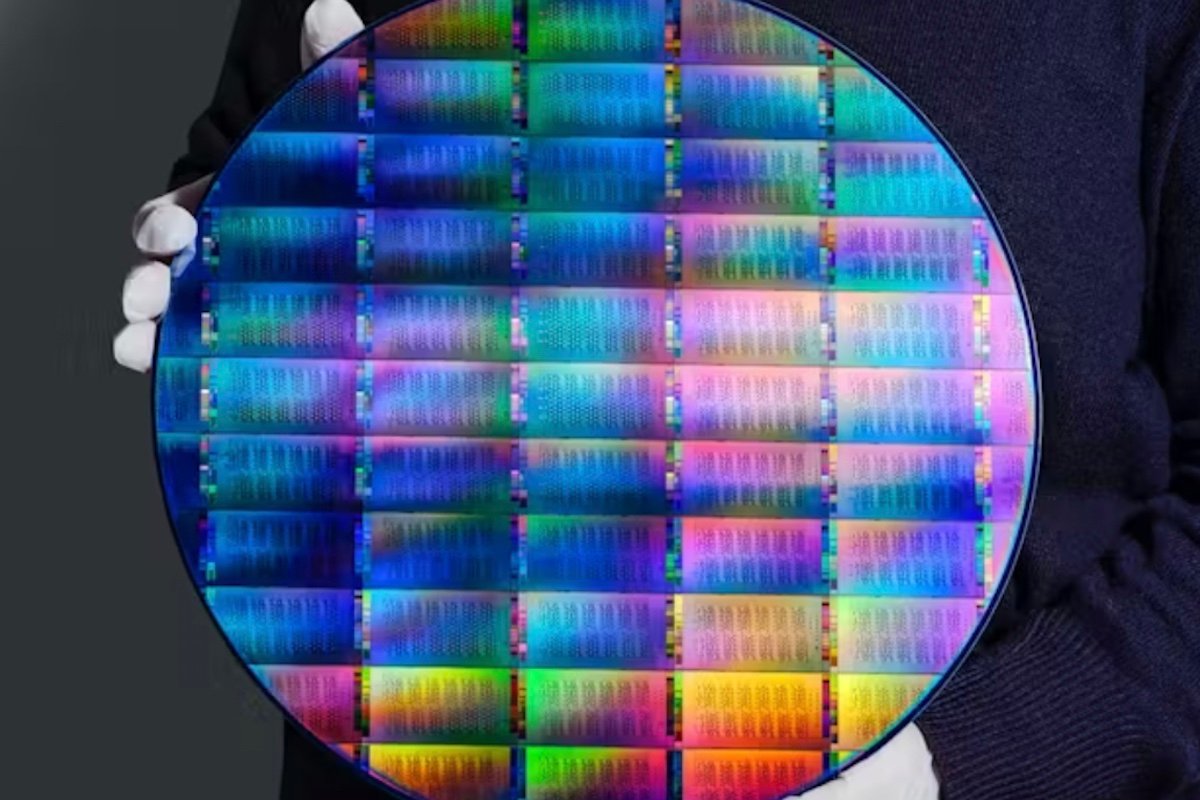
Late last year, IBM revealed a 120-qubit chip which it hopes will demonstrate a quantum advantage for some tasks.
Google recently too DESIGNATED it planned to accelerate its move to adopt encryption techniques that should be secure against quantum computers, known as post-quantum cryptography.
Alongside these tech giants, newer approaches are also flourishing. PsiQuantum is using light-based qubits and traditional chip manufacturing technology. Experimental platforms such as neutral atom systems have demonstrated control over thousands of qubits in laboratory settings.
In response, standards bodies and national agencies are setting increasingly concrete timelines to move away from conventional encryption systems that are vulnerable to quantum attacks.
In the United States, the National Institute of Standards and Technology (NIST) has proposed a transition away from vulnerable quantum cryptography, with the migration largely completed by 2035.
In Australia, it is issued by the Australian Signals Directorate similar instructionsurging organizations to start planning immediately and move to post-quantum cryptography by 2030.
Algorithms make blocking faster
Hardware is only half the story. Equally important are advances in quantum algorithms—ways to use quantum computers to attack encryption.
Much interest in the development of quantum computers was driven by Discovery of Peter Shor 1994 of an algorithm that showed how quantum computers could efficiently find the prime factors of very large numbers. This mathematical trick is exactly what you need to break the common RSA encryption method.
For decades, it was believed that a quantum computer would need millions of physical qubits to pose a threat to real-world encryption. This is much larger than current systems, so the threat felt easily distant.
That picture is now changing.
In March 2026, Google’s Quantum AI team published a detailed study showing that it may take far fewer resources to attack another type of encryption that uses mathematical objects called elliptic curves.
This is what systems including Bitcoin and Ethereum use – and the study shows how a quantum computer with less than half a million physical qubits may be able to crack it in minutes.
This is still a long way beyond current quantum computers, but about ten times less than previous estimates.
at the same time, a March 2026 preprint from a Caltech–Berkeley–Oratomic collaboration explores what might be possible using quantum computers with neutral atoms. The researchers estimate that Shor’s algorithm can be implemented with 10,000-20,000 atomic qubits.
In one design they propose, a system with about 26,000 qubits could crack Bitcoin encryption in a few days, while harder problems like the RSA method with a 2048-bit key would take more time and resources.
Simply put: code breakers are becoming more efficient. Advances in algorithms and design are constantly lowering the bar for quantum attacks, even before large-scale hardware exists.
What now?
So what does this mean in practice? First, there is no immediate catastrophe – today’s cryptography will not break overnight. But the direction of travel is clear. Any improvement in hardware or algorithms narrows the gap between current capabilities and useful quantum cracking machines.
Second, durable protections already exist. NIST has standardized some post-quantum cryptographic algorithmswhich are believed to be immune to quantum attacks.
Tech companies are starting to deploy these in hybrid ways: Google Chrome and Cloudflare, for example, already support post-quantum protection in some protocols and services.
Systems that rely heavily on elliptic curve cryptography – including cryptocurrencies and many secure communication protocols – will need special attention. of Google last job explicitly states the need to migrate blockchain systems to post-quantum schemes.
Finally, this is a two-front contest. It is not enough to track progress in quantum hardware alone. Advances in algorithms and bug fixes can be just as important, and recent results show that these improvements can significantly reduce the estimated cost of attacks.
Any new headline about reduced cube counts or faster quantum algorithms should be understood for what it is: another step toward a future where today’s cryptographic assumptions no longer hold.
The only reliable defense is to move – deliberately but firmly – towards secure quantum cryptography.
Craig Costello is a professor, School of Computer Science, Queensland University of Technology
This article was reprinted from Conversation under a Creative Commons license. Read on original article.